Palo Alto Networks Technology
Unique Identification Technologies Enable Palo Alto Networks’ Next-Generation Firewall
Palo Alto Networks safely enables your applications, users and content through innovative, tightly integrated technologies and services. Our firewalls determine an application's identity and classify it across all ports. Next, the application and user are assigned a safe enablement policy, which will apply to all of your users and protect your network against all type of threats from the application – both known and unknown.
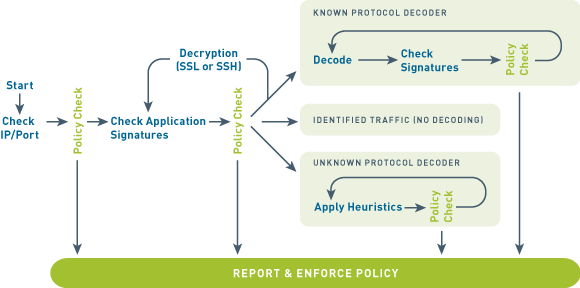
App-ID
Traffic classification is at the heart of any firewall, because your classifications form the basis of your security policies. Traditional firewalls classify traffic by port and protocol. At one point, this was a satisfactory mechanism for securing the perimeter. Not anymore.
If you still use a port-based firewall it is easy for applications to bypass it by:
- Hopping ports
- Using SSL and SSH
- Sneaking across port 80
- Using non-standard ports
Simply put, the traffic classification limitations of port-based firewalls make them unable to protect today's network. That's why we developed App-ID™, a patent-pending traffic classification system only available in Palo Alto Networks firewalls. App-ID™ instantly applies multiple classification mechanisms to your network traffic stream, as soon as the device sees it, to accurately identify applications.
Content-ID
Content-ID gives you a real-time threat prevention engine, combined with a comprehensive URL database, and elements of application identification to:
- Limit unauthorized data and file transfers
- Detect and block exploits, malware and malware communications
- Control unapproved web surfing
The application visibility and control of App-ID, coupled with the content inspection enabled by Content-ID, empowers your IT team to regain control over your application traffic and related content.
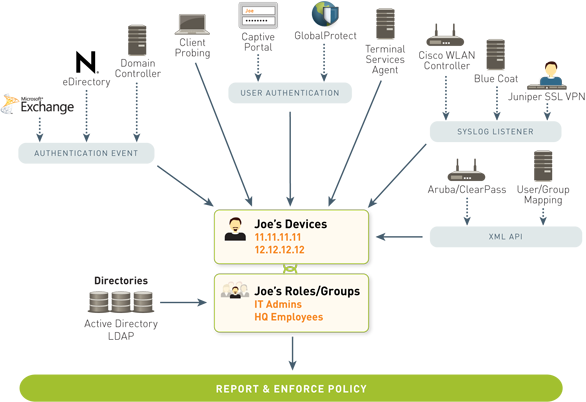
User-ID
User-ID seamlessly integrates Palo Alto Networks next-generation firewalls with a wide range of user repositories and terminal services environments. Depending on your network environment, there are a variety of ways you can map a user's identity to an IP address. Some of these include:
- Authentication events
- User authentication
- Terminal services monitoring
- Client probing
- Directory services integration
- Syslog Listener and a powerful XML API
The user identity, when tied to the application activity, provides you with more complete visibility into usage patterns, greater policy control, and more granular logging, reporting and forensics capabilities.
Purpose-built Platform
Multi-Gbps throughput is enabled through function-specific processing for networking, security, threat prevention and management, which are tightly integrated with a single pass software engine to maximize throughput. A 10Gbps data plane smoothes traffic flow between processors while the physical separation of control and data plane ensures that management access is always available, irrespective of traffic load.
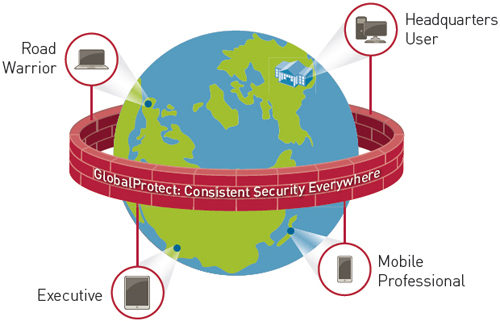
GlobalProtect
GlobalProtect provides a comprehensive security solution for mobile devices built upon the technologies of the Palo Alto Networks enterprise security platform and tailored to address mobile requirements. It delivers unprecedented levels of integration to deliver a unique solution that combines technology, global intelligence and policy enforcement over mobile apps and threats. These principles allow businesses to provide a safe environment for applications and data while still permitting users to enjoy the native user experience of their preferred device.
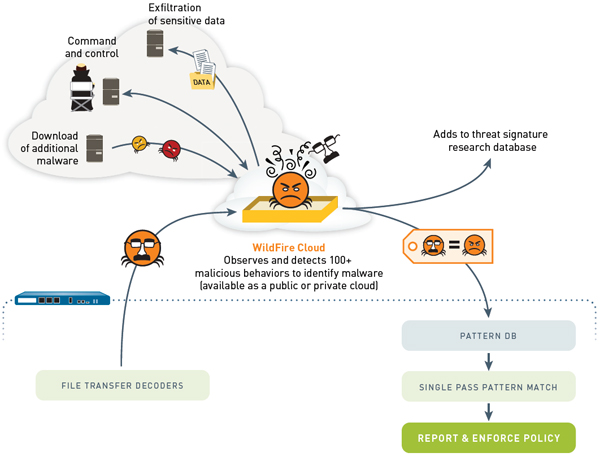
WildFire
WildFireTM simplifies an organization’s response to the most dangerous threats—automatically detecting unknown malware and quickly preventing threats before organizations are compromised. Unlike legacy security solutions, WildFire quickly identifies and stops these advanced attacks without requiring manual human intervention or costly Incidence Response (IR) services after the fact.
- Unified hybrid cloud architecture, either deployed through the public cloud, or via a private cloud appliance that maintains all data on the local network.
- Dynamic analysis of suspicious content in a cloud-based virtual environment to discover unknown threats.
- Automatic creation and enforcement of best-in-class content-based malware protections.
- Link detection in email, proactively blocking access to malicious websites.
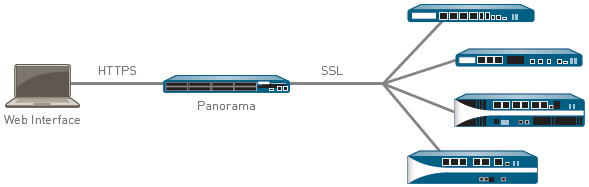
Panorama
Panorama enables you to centrally manage the process of configuring devices, deploying security policies, performing forensic analysis, and generating reports across your entire network of our next-generation firewalls. Available as either a virtual appliance or a dedicated management platform, Panorama and the individual device management interfaces share the same web-based look and feel, ensuring workflow consistency while minimizing any learning curve or delay in executing the task at hand.